On the evening of May 5th, 2026, large parts of the German web briefly went dark.
For a few hours, anyone trying to load a .de address through a major DNS resolver got errors instead of websites. Bahn.de, Amazon.de, and Spiegel.de were among the affected.
Major brands like Telekom, DHL, and Sparkassen felt it too, along with hosting providers Hetzner, Strato, and Ionos. The cause sat well below most sites’ own infrastructure: a single broken cryptographic record at DENIC, the registry that runs the .de top-level domain.
From inside our monitoring network, the impact was immediate and concentrated.
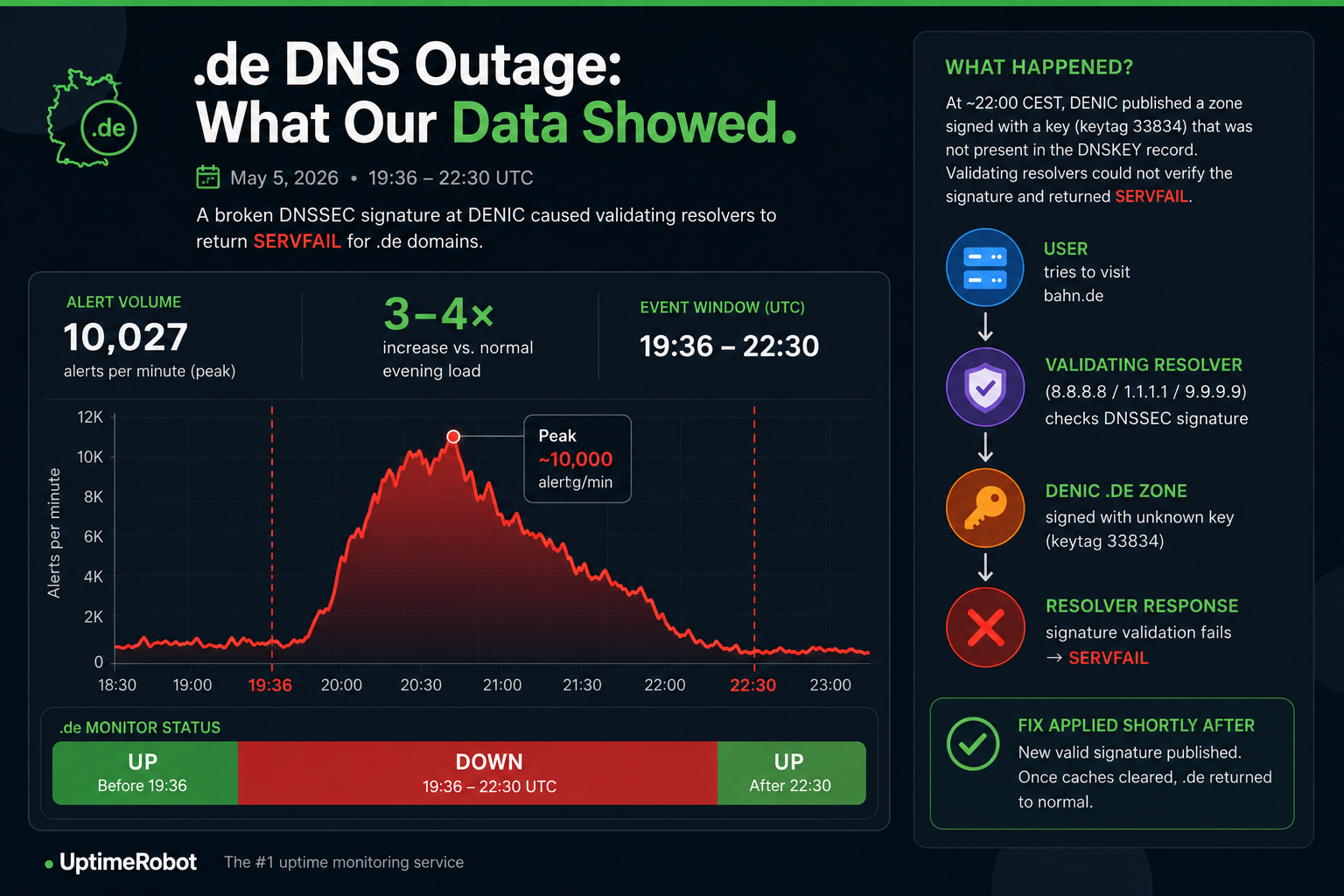
Alert volume on .de monitors jumped to roughly 3-4x the usual evening load, peaking at around 10,000 alerts per minute.
The spike ran from 19:36 to 22:30 UTC, which lines up with the window during which DENIC’s broken signature was being served before resolver caches finished clearing.
What happened at DENIC (the short version)
DENIC has posted a status update on their X profile (DENIC status page), and a deeper post-mortem will likely follow in the next few days. In the meantime, the picture from independent technical write-ups is fairly consistent.
The .de zone uses DNSSEC, the security layer that lets resolvers verify DNS answers cryptographically. Around 22:00 CEST on May 5, DENIC pushed zone data signed with a Zone Signing Key (keytag 33834) that was not present in the matching DNSKEY record. From a resolver’s point of view, the response carried a signature that could not be verified, so the only safe behavior was to refuse the answer and return SERVFAIL.
That single mismatch had outsized impact. Validating resolvers including Google Public DNS (8.8.8.8), Cloudflare (1.1.1.1), and Quad9 (9.9.9.9) all rejected responses for .de.
This meant most users on consumer ISPs and cloud networks could not resolve any .de addresses at all. Resolvers that skipped DNSSEC validation, or that still had cached entries, kept working. That is why some people saw nothing wrong while others could not reach a single German site.
DENIC re-signed the affected record with a valid key shortly after. Once stale signatures cleared from resolver caches, .de went back to normal. According to community reporting, the previous comparable .de-wide event was in 2010, which puts this in the once-in-a-decade-plus category.
This was not a cyberattack, but an operational failure during a routine signing key rollover, and it is a clear reminder of how fragile the layers underneath the visible web actually are.
What we saw across the internet
When DENIC’s signed responses started failing validation, our monitoring data reacted within seconds.
A large concentration of monitors pointing at .de targets flipped from UP to DOWN almost simultaneously. Inside the dashboard, the pattern looked less like a single clean outage and more like a hard cliff at 22:00 CEST followed by a long tail as resolvers worked through their caches. Some monitors recovered within minutes once a fresh lookup hit a healthy resolver path. Others stayed in the failed state until DENIC’s fix had fully propagated.
Alert volume on .de monitors went up sharply during the event window. Support also saw an uptick in tickets asking why German sites had triggered downtime alerts when “the server was clearly fine.” The short answer: the servers were fine, but no one could find them.
Pro tip: If your domain runs on a country-code TLD like .de, your reachability is only as strong as the registry running it. Pair standard HTTP monitoring with DNS-level checks so that a problem one layer below the website still surfaces as a clear, actionable alert.
Final thoughts
Country-code TLDs feel like the most boring part of the stack, right up until they break. A single bad signature in one zone took millions of websites offline at once, and most of those sites had no warning, no fault of their own, and no way to fix the issue from their side.
The hard part is knowing, in the first 60 seconds, whether the problem is yours, your provider’s, or somewhere upstream entirely. Everything depends on the answer to that question: who you wake up, what you tell customers, and how fast you can move.
That is exactly where multi-location monitoring earns its keep. UptimeRobot checks your sites from multiple regions worldwide, so you can see at a glance whether a .de domain is failing from European resolvers but resolving from elsewhere, whether the issue is global, or whether it is just one region acting up.
Different vantage points, different DNS resolver behavior, one dashboard. You get the answer in seconds instead of guessing your way through a war room.
Pair that with DNS monitoring on the domains you care about most, and you stop finding out about registry-level incidents from angry customers on social media.
Get 50 monitors with 5-minute checks, free, no credit card required.
